A massive attack is currently taking place and could potentially affect all decentralized applications (dApps) integrating Ledger’s connect kit. It is currently recommended not to visit ANY website offering the Web3 wallet connection functionality
MAJ 15:18: Ledger’s update is being rolled out, according to the firm. Ledger also said that a “full report” will be published as soon as it’s ready.
UPDATE 15:06: Banteg published a message stating that Ledger had implemented an update and that the malicious code had been deleted. However, it is still recommended not to interact with any Wallet-enabled application, as propagation may take some time.
UPDATE 15:03: According to Igor Igamberdiev, the malicious code was implemented this morning at around 8:44 a.m., so it’s likely (but not certain) that the wallets potentially at risk are those that interacted with Ledger’s Connect Kit after that time.
UPDATE 14:57: According to on-chain investigator ZachXBT, over $610,000 has already been stolen via the flaw. According to Arkham Intelligence data, the address cited by ZachXBT would have sent funds to Angel Drainer, whose wallet totals more than $1 million.
A major attack is underway
This could be one of the biggest attacks ever to take place in the Web3 ecosystem: it seems that all decentralized applications (dApps) integrating the Ledger connection tool have been infected, and their code has been replaced by a drain functionality.
The flaw was first reported by the Sushi protocol, which took its site offline as a security measure, and which informs us that the problem originated with Ledger:
Urgent Security Alert
We’ve identified a critical issue the ledger connector has been compromised, potentially allowing the injection of malicious code affecting various dApps.
If you have the Sushi page open and see an unexpected ‘Connect Wallet’ pop-up, DO NOT… https://t.co/alGVbnPfHW
– Sushi.com (@SushiSwap) December 14, 2023
Matthew Lilley, Sushi’s CTO, has stated that the flaw did indeed originate at Ledger, and more specifically in their Connect Kit responsible for managing interaction with decentralized applications. The list of potentially affected applications can be found here. It includes all applications integrating this Ledger functionality
ANY dApp which makes use of LedgerHQ/connect-kit is vulnerable. Don’t use ANY dApps until further notice. This isn’t a single isolated attack, it’s a large-scale attack on multiple dApps. https://t.co/a3brXNQSx9
– I’m Software (@MatthewLilley) December 14, 2023
This attack is all the more devious in that it has also infected sites allowing the revocation of authorizations granted to smart contracts, such as Revoke.Cash, which has also taken its site offline to mitigate potential losses to its users. Revoke.Cash recommends that you do NOT use any site that connects to a Web3 wallet.
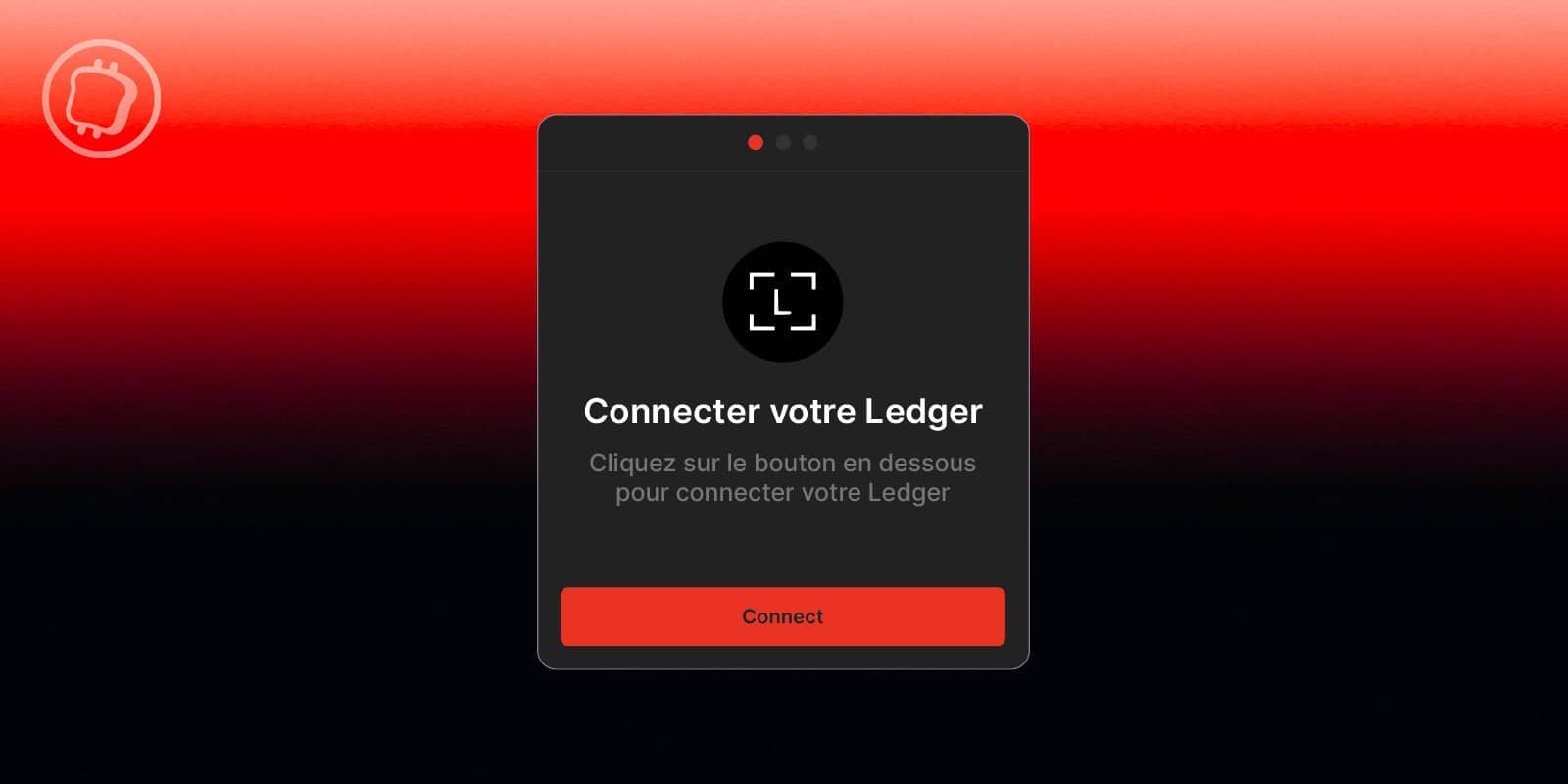
For your information, here is a preview of the window containing the malicious code:
An example of the deployed code (the window appears above the actual connection): https://t.co/7J34ArOTLR
– OAK (@oak_en) December 14, 2023
Ledger issued a press release on X without providing any additional information:
We have identified and removed a malicious version of the Ledger Connect Kit.
A genuine version is being pushed to replace the malicious file now. Do not interact with any dApps for the moment. We will keep you informed as the situation evolves.
Your Ledger device and…
– Ledger (@Ledger) December 14, 2023